How defense in depth can help cybersecurity teams win the big game:
No single control can stop every offensive play, but a well-coordinated and responsive cyber defense can.

When the Seattle Seahawks and the New England Patriots take the field for Super Bowl LX, their defensive lines will be tested. How well they read and respond to the opposing offense will determine who stops the ball — and who doesn’t.
Cybersecurity teams don’t need to be football fans to see the parallel. Winning defense — on the field or in the digital arena — depends on coordination and anticipation. Like an NFL defensive line, a cybersecurity team must layer its defenses to close gaps and stop big plays.
The Microsoft Digital Defense Report 2025 echoes this sentiment. It notes, “Effective defense isn’t just patching fast — it’s expecting gaps and building layers of resilience through anomaly detection, behavior-based analytics, and hardening high-risk assets.”
That’s where defense in depth (DiD) comes in — an age-old approach that turns individual controls into a unified game plan.
SHI and Stratascale, SHI’s cybersecurity division, have huddled up with thousands of customers to implement winning DiD strategies.
Let’s go to the whiteboard and diagram the play.
What exactly is DiD and why is it a winning strategy?
DiD didn’t originate in cybersecurity — it began as a military tactic. In battle, armies learned a single line wasn’t enough to stop an advancing force. In response, they built layers: trenches, walls, and fallback positions to slow attackers.
DiD’s application in cybersecurity follows the same principle. Instead of a single safeguard, DiD layers defenses so others can slow or contain an attack if one fails.
Why is this critical today? Attackers often exploit simple weaknesses rather than executing sophisticated schemes. As the same Microsoft Digital Defense Report 2025 warns, “a third of attackers use crude tactics as the easy path into an organization’s exposed footprint.”
Bitdefender’s Official 2025 Cybersecurity Assessment Report reinforces the need for DiD. It states, “True protection demands a layered approach, where prevention, detection, and response work together seamlessly to stop threats before, during, and after they strike.”
The key to successful DiD? Coordination, configuration, and coverage
DiD is not just about tool accumulation. In reality, many organizations have sufficient tools in place but make missteps in configuring and coordinating them. Additionally, many organizations actually have too many tools, which makes coordination even harder.
To illustrate, consider the importance of DiD through the lens of a recent cyberattack on a U.S. electric utility cooperative detailed in ACSMI’s State of Ransomware 2025 report.
The breakdown of a cybersecurity defense
The attack began when the Royal Ransomware Syndicate sent a phishing email to a contractor at the utility cooperative.
Even with controls in place that should have contained a phishing attempt (EDR, SOC monitoring, and cyber insurance), two gaps aligned. First, the contractor shared their credentials. Second, a misconfigured firewall failed to block the attacker’s request for remote access.
Once inside, the attackers ran a living-off-the-land (LOTL) attack that used native Windows tools to stay hidden, bypass alerts, and encrypt the cooperative’s control system data.
When the breach was finally detected, recovery efforts fell short. Backups hadn’t been tested in six months, and incident response plans required approvals from four departments, slowing containment by 16 hours.
Eventually, the attackers reached the cooperative’s Supervisory Control and Data Acquisition (SCADA) controls and forced power outages across three counties.
With leverage in hand, the attackers made their demands — a $3.1M ransom payment, which the organization paid in full.
Collectively, this chain of events shows how quickly small gaps can compound when defensive layers don’t hold. Next, let’s look at how a layered defense can prevent one or two points of failure from turning into a full-scale compromise.
The six layers of a winning cyber defense, guided by the NIST Cybersecurity Framework (CSF) 2.0
In 2024, NIST released the NIST CSF 2.0 Framework — introducing a sixth function that elevated governance to a core role.
The framework helps clarify how each DiD layer fits into a tiered defensive structure.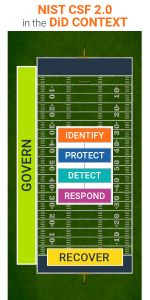
1) Govern
This function defines the organization’s cybersecurity strategy, roles, and policies, and ensures they align with the overall risk management strategy. It also guides all other functions.
On the field: Think of this as your coaching staff and playbook — where you set the game plan, pick your players, assign positions, and determine your goals.
Action categories: Risk management policy, control baselines, decision rights, and cross-silo incident authority.
2) Identify
The purpose of this function is to clarify the organization’s assets, suppliers, and third-party risks so teams can prioritize effort in line with mission and risk strategy.
On the field: Think of this as your scouting report — where you study the other team, the matchups, and the plays they’re likely to run. It also doubles as a real-time function, helping coordinators and defensive lines read the offense’s formation.
Action categories: Automated asset discovery, data classification, red teams, attack surface management, and vendor risk assessments.
3) Protect
This stage focuses on applying safeguards that protect prioritized assets and reduce the likelihood and impact of cybersecurity events.
On the field: Think of this as blocking and tackling at the line of scrimmage — where your defenders must stop the offense from capitalizing on the quick slant or easy run up the middle.
Action categories: Network segmentation, least-privilege access, MFA and conditional access, encryption, secure baselines, and patch configuration management.
4) Detect
Here, organizations need timely detection and analysis of anomalies or indicators of compromise to uncover attacks and support effective response.
On the field: Think of this as zone coverage and game film study come to life — where your defense needs to recognize patterns and close space before the receiver breaks free.
Action categories: EDR and XDR, SIEM and UEBA, deception hosts, identity threat detection, canary tokens, and lateral movement analytics.
5) Respond
This function centers on taking swift, coordinated actions that contain and mitigate detected incidents through analysis, management, and communication.
On the field: Think of this as conducting pursuit drills — where the defense needs to chase down and limit the offensive damage, by cutting off angles and stopping the drive.
Action categories: Automated containment (quarantine, token revocation), PAM session kill, egress blocks, incident communications, and legal and regulatory steps.
6) Recover
The goal of this function is to quickly restore affected assets and operations following a cyber incident, while maintaining clear communication throughout the recovery process.
On the field: Think of this as resetting after a score — where special teams execute the return, coaches adjust, and the defense comes back stronger after refueling on electrolytes.
Action categories: Offline and immutable backups, tested restore runbooks, failover procedures, RTO and RPO targets, and post-incident reviews.
Need a defensive coordinator on your sidelines?
SHI’s and Stratascale’s unbiased experts have studied decades of tape and can help you shape a strategy, close security gaps, and select the right solutions for your organization.
1) Start by assessing your security posture
SHI offers a free Security Posture Review to map your assets, identify vulnerabilities, and make a plan to close vulnerability gaps.
2) Book or build the right executive briefing for your organization
Gain clarity on your cybersecurity priorities by choosing a topical or tailored session from SHI’s executive briefing catalog, like “Risk Registers: Beginning the Cyber Risk Journey” or “Data Continuity Strategies”.
3) Strengthen your response readiness
Prepare your organization to defend year-round with Stratascale’s Incident Response Retainer, which provides rapid access to expert responders, deep forensic analysis, and optional tabletop exercises.
Cybersecurity is a team sport — and it’s game day, every day
Like offensive teams in football, cybercriminals are constantly on the attack, adjusting their playbook and forcing your defense to adapt.
And just as 11 random football players don’t make a defense, a pile of tools doesn’t make a cybersecurity strategy. Without proper configuration, testing, and accurate prioritization of each defensive layer, even well-equipped organizations can remain vulnerable.
We don’t know who will win on Super Bowl Sunday. But the smartest approach — in football and in cybersecurity — comes back to the words of one of college football’s winningest coaches. As the University of Alabama’s Paul “Bear” Bryant once said, “Offense sells tickets, but defense wins championships.”
NEXT STEPS
Have the tool depth, but need help with the prioritization? Have some defense but lack depth? Connect with one of our cybersecurity experts today about how a DiD approach can strengthen your organization.




