6 best practices for application security

Organizations across the globe scrambled to enhance their digital capabilities in the wake of COVID-19, using modified applications, new applications, and new websites to bring business online as quickly as possible. Attackers have been capitalizing on the chaos.
The FBI reported a 400% spike in cyberattacks since the start of the pandemic. With resources strained by the financial and operational consequences of the crisis, attacks that exploit system and application vulnerabilities are a critical concern.
According to a Veracode software security report [Link removed as of January 2025], 83% of applications have at least one flaw, and 20% have high-severity flaws. Now more than ever before, validating and reinforcing your application security posture should be a top priority.
While security weaknesses in the applications we build and buy are a near certainty, the ability to find and fix them can be elusive. Here are six recommendations for effective application security.
1. Take a DevSecOps approach
A GitLab survey revealed 68% of security professionals think it’s a developer’s job to write secure code, but less than half of developers can spot security holes. At the same time, nearly 70% of developers said that while they’re expected to write secure code, they get little guidance or help.
To tackle this problem head on, security needs to be embedded into DevOps.
This requires a cultural change and leadership that fosters training. Make it clear that everyone is responsible for security and avoid the blame game. Provide development, security, and IT operations teams with cross-skilling opportunities so you can prioritize secure code creation and discover vulnerabilities earlier in the pipeline. This will yield better results and help reduce friction between security and developers.
The Open Web Application Security Project (OWASP) provides helpful resources. The OWASP Top 10 list can help you maintain awareness of the most critical security risks to web applications, and the OWASP Secure Coding Practices Checklist can be used as a secure coding kickstart tool and easy reference for addressing the intersection of coding and security.
2. Automate testing in the software development life cycle (SDLC)
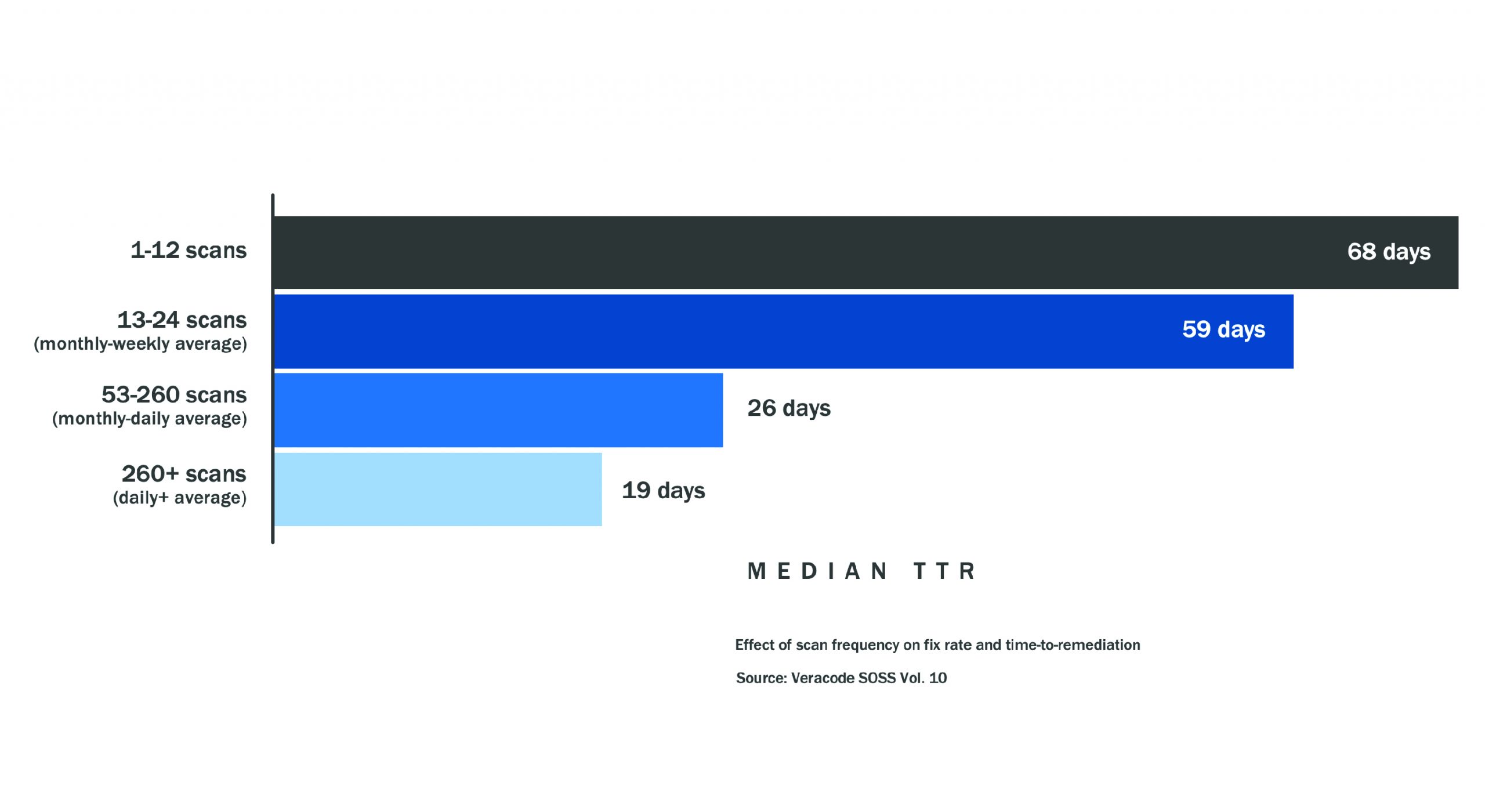
The longer vulnerabilities remain, the less chance there is that they’ll be addressed. Frequent application security testing (AST) will boost your efforts.
The mean time to remediation (MTTR) — the average time it takes to fix flaws — for applications scanned less than once per month stands at 68 days. Organizations with an average scan frequency of daily or more (260+ scans) can knock that statistic down to 19 days. That’s a 72% reduction in MTTR.
 The key is automation. Static application security testing tools (SAST) can be incorporated into developers’ integrated development environment (IDE), allowing them to test code as they develop it.
The key is automation. Static application security testing tools (SAST) can be incorporated into developers’ integrated development environment (IDE), allowing them to test code as they develop it.
According to Gartner, by 2025, organizations will speed up their remediation of coding vulnerabilities identified by SAST by 30% with code suggestions applied from automated solutions, up from less than 1% today, reducing time spent fixing bugs by 50%.
AST can be delivered as a tool or as a subscription service. Many vendors offer both options.
3. Manage the open source you use
Developers often use open source components as their foundation, creating applications that contain only a small percentage of custom code. In fact, 96% of the total codebases analyzed for a recent application security report contained open source, and 76% of codebases contained at least one open source vulnerability.
Unlike commercial software, where updates are automatically “pushed” to users, open source has a “pull” support model. Users are responsible for keeping track of vulnerabilities, fixes, and updates on their own. It’s critical that you know which open source components you’re using so you can address vulnerabilities as they’re announced.
This requires an up-to-date, accurate inventory — i.e., a software bill of materials (BOM) — that includes all open source components, the versions in use, and the locations for each project in use or in development. It should also feature the libraries your code is calling to and the libraries they’re linked to.
Software composition analysis (SCA) solutions facilitate this effort. They analyze open source and commercial code, provide visibility across your application landscape, and aid in building an inventory of open source components to identify vulnerabilities and highlight any liabilities in license agreements.
4. Inspect traffic with a web application firewall (WAF)
WAFs provide an important line of defense for critical applications and data.
They filter, monitor, and block any malicious HTTP/HTTPS traffic traveling to the web application. They also prevent unauthorized data from leaving the application by adhering to policies that help determine which traffic is malicious and which traffic is safe. A WAF operates similarly to a proxy server that acts as an intermediary to protect the identity of a client, except in reverse — called a reverse proxy. It acts as an intermediary that protects the web application server.
Used in combination with application programming interface (API) management and identity and access management (IAM) solutions, WAFs can help you protect the APIs that connect services and transfer data, which are increasingly targeted by attackers. Make sure that WAFs are tuned specifically for the application being protected, as default configurations are too lax.
5. Implement least privilege
A recent study found 74% of data breaches involve access to privileged accounts. To reduce the risk of attackers gaining access to critical applications and data, give users only the bare minimum privileges needed to do their jobs, and centrally manage services accounts.
Privileged access management (PAM) controls can help you grant least privilege access based on who’s requesting it, the context of the request, and the risk of the access environment without downtime or loss of productivity. When individual accounts need to execute privileged tasks, PAM solutions allow you to grant access that’s confined to the scope and time required to complete the activity, and remove that access afterward.
6. Strengthen threat and vulnerability management
In 2019, 60% of data breaches involved unpatched vulnerabilities. To ensure good cyber hygiene, implement solid vulnerability assessment and patch management processes to identify vulnerabilities and link them to patches that can remediate them.
Be sure to run vulnerability scans both before and after patching to verify success. Once you feel you’ve remediated enough findings to improve your security posture, engage penetration testers to examine the environment with an “ethical attack” to reveal the effectiveness of your controls and ensure malicious actors can’t penetrate your applications.
Mature your application security program
Applications are the foundation of today’s enterprise, but they have vulnerabilities waiting to be exploited.
As we navigate our new work-from-home world and the threats that come with it, securing the software that runs business has never been more important. With a DevSecOps approach, the right solutions, least privilege access control, and effective threat and vulnerability management, you can secure the applications you build and buy to better protect data and reduce risk.
Anne Grahn and Brad Bowers contributed to this post.





